experience
From hybrid labor to smarter workspaces, combining technology and touchpoints to provide exceptional experiences.
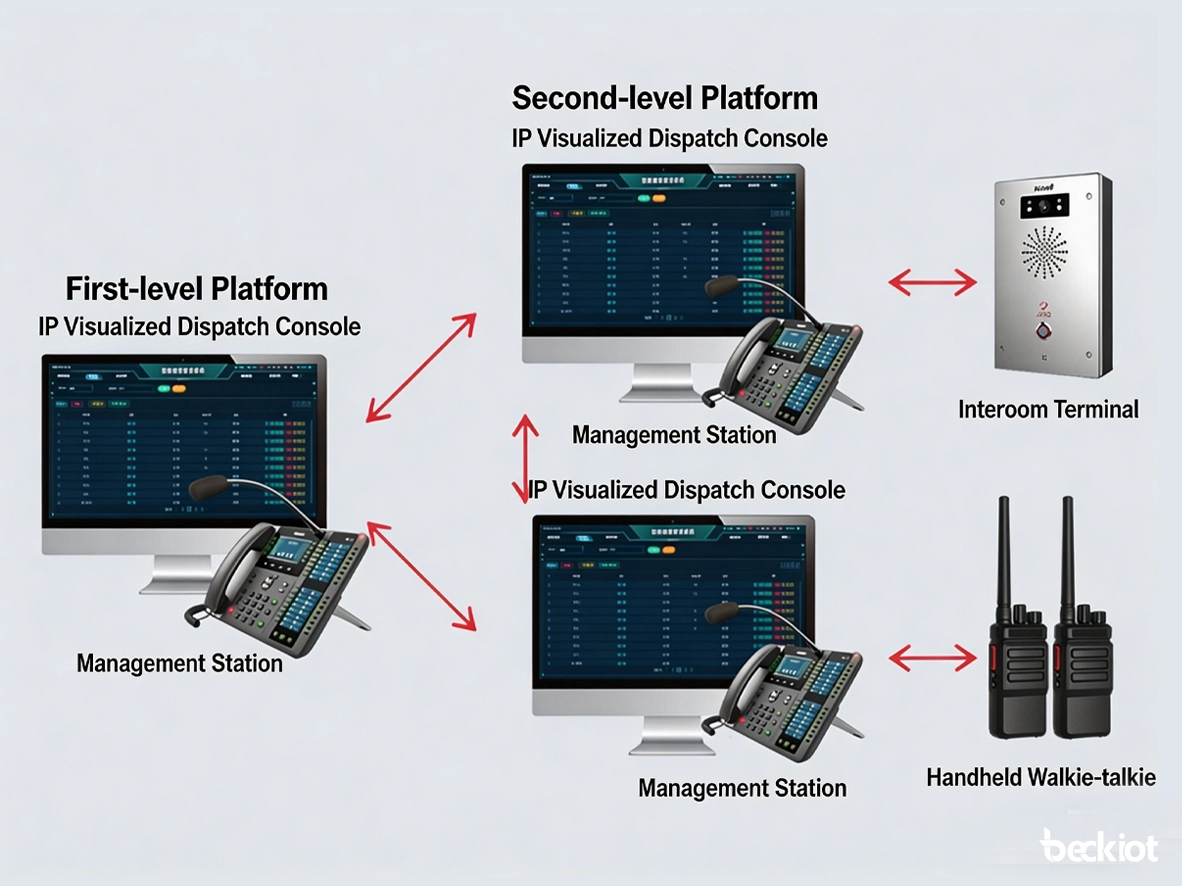
View DetailsEmergency Communication
command and dispatch
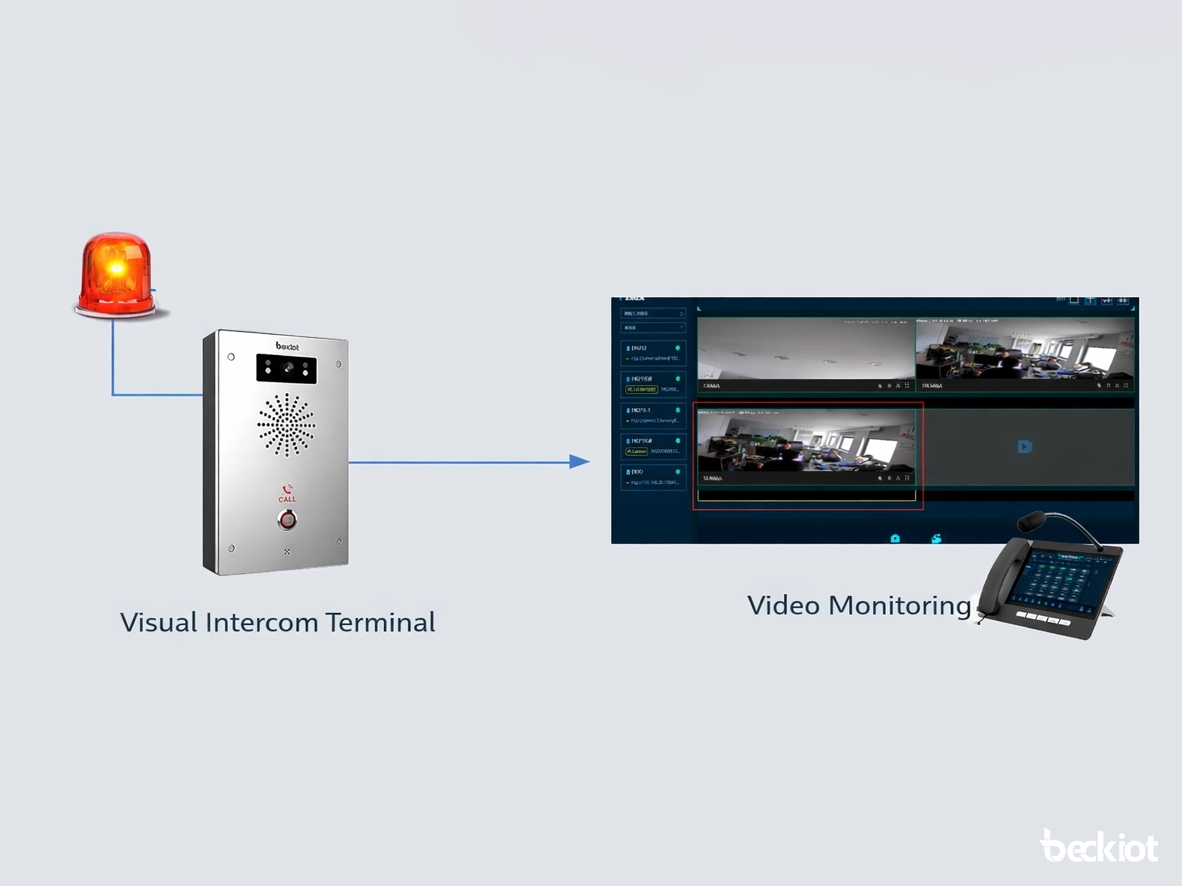
Alarm System
IP PBX
product
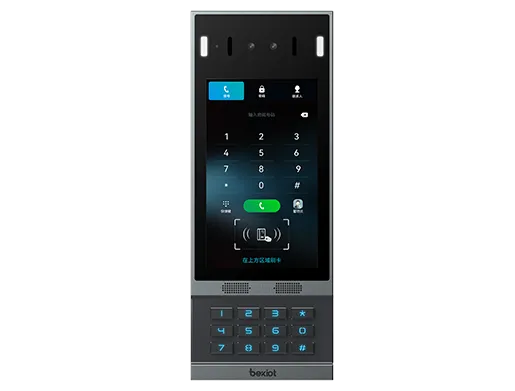
Using Baker's top-notch technology to create exceptional experiences for people, environments, and things.
View Detailsindustrial telephone
dispatch console
IP phone
SIP intercom
touchpoint
In addition to terminal devices, all personnel, places, and things connected to the network should also be considered.
View Detailsindustry
resource
Understand best practices, explore innovative solutions, and establish connections with other partners throughout the Baker community.