IPsec encryption is a common way of describing the security protections delivered by Internet Protocol Security (IPsec). In practice, IPsec is not just an encryption feature. It is a security architecture for IP networks that can provide confidentiality, integrity, authentication, replay protection, and policy-based traffic control at the network layer. That is why IPsec remains important in enterprise VPNs, branch interconnection, cloud networking, and many infrastructure environments where security needs to be built into the IP path itself rather than added only at the application layer.
One reason IPsec still matters is that it works below most applications. A web browser might use HTTPS, an email platform might use TLS, and a voice platform might use SRTP, but IPsec protects IP traffic more generally. It can secure communication between hosts, between security gateways, or between a host and a gateway. That makes it useful when you want to protect many applications at once without redesigning each application separately.

IPsec is a network-layer security framework that can protect traffic between hosts, gateways, or mixed host-to-gateway environments.
What Is IPsec Encryption?
IPsec stands for Internet Protocol Security. It is a suite of protocols and rules designed to secure traffic at the IP layer. In other words, IPsec sits closer to the network than application-specific security mechanisms. Instead of protecting only a web session or only a file transfer, IPsec can protect packets for many kinds of services as long as policy allows those packets into an IPsec security association.
The phrase IPsec encryption is convenient, but slightly incomplete. Encryption is only one part of the picture. Depending on how IPsec is configured, it may provide:
- confidentiality for packet payloads,
- data origin authentication,
- connectionless integrity,
- anti-replay protection, and
- traffic selection and policy enforcement.
In real deployments, these protections are most often associated with ESP, or Encapsulating Security Payload, together with IKEv2, the key management protocol used to authenticate peers and establish the security associations that define how packets will be protected.
How IPsec Works
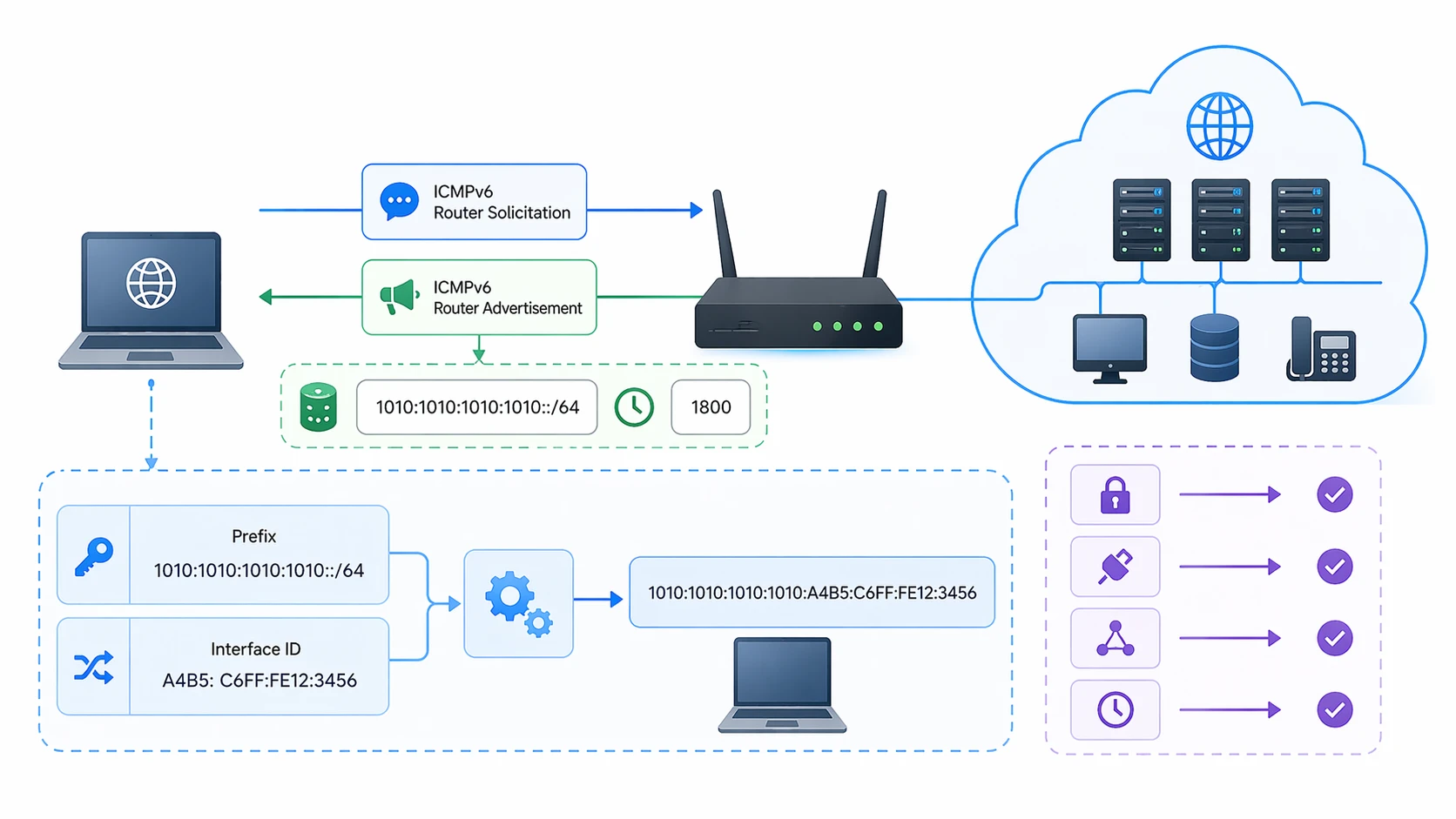
At a practical level, IPsec works by deciding which packets should be protected, negotiating the security parameters for those packets, and then applying the selected security services as traffic moves across the network.
1. Traffic selection and policy
An IPsec implementation first needs rules that determine what traffic should be protected. Those rules are usually based on source and destination addresses, protocols, ports, interfaces, peer identities, or broader network policies. In enterprise language, this is often the interesting traffic that must enter an IPsec tunnel.
Under the IPsec architecture, policy and state are not accidental details. They are fundamental. The system must know which traffic qualifies and how that traffic should be handled. Some traffic may be discarded, some may bypass IPsec, and some must be protected before it is sent.
2. Peer authentication and key exchange
Once protected traffic is identified, the two peers need to agree on how to secure it. That job is usually handled by IKEv2. The peers authenticate each other, negotiate cryptographic parameters, derive shared keys, and establish one or more security associations. These SAs define the algorithms, keys, lifetimes, modes, selectors, and related parameters for the protected session.
Authentication can be based on pre-shared keys, digital certificates, or other supported methods. In small deployments, pre-shared keys are common because they are easy to set up. In larger or more security-sensitive environments, certificates are often preferred because they scale better and support stronger identity management.
3. Packet protection with ESP or AH
After the security association is established, IPsec protects packets using one of its protocol mechanisms. In modern deployments, ESP is by far the more common choice. ESP can provide confidentiality and may also provide integrity, authentication, anti-replay protection, and limited traffic flow confidentiality. Because it covers the most important real-world use cases, ESP is the protocol most people mean when they talk about IPsec tunnels.
AH, or Authentication Header, is another IPsec protocol. AH is designed to provide authentication and integrity services, but it does not provide confidentiality. It also protects more of the immutable IP header fields than ESP in transport mode. In practice, AH is used less often, especially in environments where address translation and tunnel interoperability matter more than header coverage.
4. Ongoing maintenance
IPsec sessions are not set up once and then forgotten forever. Keys and SAs have lifetimes. Peers may rekey periodically, renegotiate algorithms, detect failures, or rebuild the tunnel after a path change. In stable networks this happens quietly in the background, but it is one reason why IPsec design is as much an operational topic as a cryptographic one.
Core IPsec Components
ESP
ESP is the workhorse of modern IPsec. It can encrypt traffic and can also provide integrity, origin authentication, and anti-replay protection. If an engineer says a firewall, router, or gateway supports IPsec VPN, that almost always implies ESP-based protection.
AH
AH focuses on authentication and integrity rather than confidentiality. It is technically important because it shows that IPsec was designed as a broader security framework rather than an encryption-only tool. Even so, many commercial deployments rely on ESP instead of AH because ESP is more flexible for common VPN scenarios.
IKEv2
IKEv2 is the negotiation and management layer. It handles peer authentication, cryptographic negotiation, key establishment, and SA maintenance. Without a robust key management process, IPsec would be far less practical at scale.
Security Associations
A security association is the active rule set for a protected traffic flow or direction. It specifies the algorithms, keys, mode, lifetimes, replay settings, and peer information used to process traffic. SAs are central to understanding IPsec because the tunnel is not just a concept; it is implemented through concrete negotiated state.
Transport Mode vs. Tunnel Mode
IPsec can operate in two main modes, and the choice affects both architecture and use case.
Transport mode
In transport mode, IPsec protects the payload of the original IP packet while leaving the original IP header in place. This mode is more direct and can be efficient when the communicating endpoints themselves run IPsec. It is typically associated with host-to-host protection, although the standards allow more nuanced scenarios in some architectures.
Tunnel mode
In tunnel mode, the original IP packet is encapsulated inside a new IP packet. This adds an outer IP header and protects the original packet as an inner payload. Tunnel mode is the familiar model for gateway-to-gateway VPNs and many host-to-gateway remote access designs. It is also the easier mental model for branch office interconnection because the tunnel behaves like a secured path between networks.
For many real deployments, tunnel mode is what people picture when they hear the term IPsec VPN. It is flexible, works well with security gateways, and aligns naturally with site-to-site designs.
Why IPsec Is Valuable
Strong network-layer protection
Because IPsec works at the IP layer, it can protect many applications at once. That makes it attractive when the goal is to secure a network path instead of modifying each application stack independently.
Broad deployment flexibility
IPsec can be used for host-to-host, gateway-to-gateway, and host-to-gateway communication. That gives network architects multiple design options depending on whether they are protecting branches, data centers, cloud links, mobile users, or selected infrastructure services.
Security beyond simple encryption
The real benefit of IPsec is not only secrecy. It also helps verify who is on the other side, whether traffic has been altered, and whether packets are being replayed. In operational terms, that makes IPsec more trustworthy than any design that relies on encryption alone.
Mature standards base
IPsec is built on long-established IETF standards and detailed implementation guidance. That maturity matters in enterprise infrastructure, especially where long lifecycle devices, multivendor interoperability, and controlled change management are important.
Common Applications of IPsec
Site-to-site VPNs
This is one of the most common uses of IPsec. Branch offices, plants, warehouses, substations, and remote campuses can connect securely over untrusted networks through IPsec tunnels between routers, firewalls, or dedicated security gateways.
Remote access
Some organizations use IPsec for secure remote user access. In this model, a laptop, tablet, or field workstation builds an IPsec tunnel to a gateway so internal applications can be reached safely across the public internet.
Data center and cloud interconnection
IPsec is widely used to secure traffic between on-premises infrastructure and cloud networks, as well as between multiple cloud or data center sites. It is especially useful when organizations need a standards-based encrypted path without depending on a single application protocol.
OT and infrastructure environments
In industrial, utility, transport, and public safety networks, IPsec can protect communications between core sites, remote stations, edge devices, and management platforms. It is often chosen when the operator wants secure routing and segmented connectivity across wide-area IP networks.

IPsec is widely used for site-to-site VPNs, remote access, cloud interconnection, and secure transport across shared IP infrastructure.
Technical Features That Matter in Real Deployments
NAT traversal
One practical challenge is that many modern networks use Network Address Translation. Standard ESP is not always friendly to NAT devices, which is why NAT traversal mechanisms are important in real-world VPN deployment. UDP encapsulation allows ESP packets to traverse NAT environments more reliably when negotiated for that purpose.
Algorithm choice
IPsec is not defined by one permanent cipher. Its security depends partly on which algorithms are enabled and how they are managed. That means design decisions must account for current cryptographic guidance, peer interoperability, performance requirements, and organizational policy.
Overhead and MTU planning
IPsec adds headers, metadata, and sometimes new encapsulation. That overhead can affect effective payload size, fragmentation behavior, and application performance if the network is not designed carefully. In production environments, MTU and MSS tuning are often as important as cryptographic settings.
Operational visibility
Encrypted tunnels improve confidentiality, but they also change how traffic is observed, filtered, and troubleshot. Teams need visibility into IKE negotiation, SA status, rekey events, route changes, packet counters, and policy mismatches. Good operations practice is essential because an IPsec tunnel can be securely configured and still fail at the routing or policy layer.
IPsec vs. TLS VPNs
IPsec and TLS-based secure access are often discussed together, but they solve the problem at different layers. TLS usually protects application sessions, while IPsec protects IP traffic more generally at the network layer. IPsec is often the better choice when you want broad network connectivity between sites or secure access to multiple internal services. TLS-based approaches may be more convenient for browser-centric or application-specific remote access scenarios.
Neither is universally better. The right choice depends on whether the security boundary should sit at the application layer or the IP layer, how much network access is required, what the user experience should look like, and what operational model the organization can support.
Deployment Considerations
- Define clear traffic selectors and avoid overly broad tunnel policies.
- Prefer strong, current algorithms and review them periodically.
- Use certificates when scale, lifecycle management, or identity assurance justify them.
- Plan for NAT traversal, MTU overhead, and routing behavior from the start.
- Monitor rekey events, peer liveness, SA counters, and tunnel failover status.
- Document whether the design is host-to-host, host-to-gateway, or gateway-to-gateway.
FAQ
Is IPsec the same as a VPN?
Not exactly. IPsec is a security framework and protocol suite, while a VPN is a broader deployment concept. Many VPNs are built with IPsec, but not all VPNs use IPsec.
Is IPsec only about encryption?
No. IPsec can provide confidentiality, integrity, authentication, anti-replay protection, and policy-based traffic handling. Encryption is important, but it is only one part of the full design.
What is the difference between ESP and AH?
ESP can provide confidentiality and may also provide integrity and authentication features. AH focuses on authentication and integrity and does not provide confidentiality. In modern deployments, ESP is generally more common.
What is the difference between transport mode and tunnel mode?
Transport mode protects the payload of the original IP packet and keeps the original IP header in place. Tunnel mode encapsulates the whole original packet inside a new outer IP packet and is widely used for gateway-based VPNs.
Where is IPsec most commonly used?
Typical uses include site-to-site VPNs, remote access, cloud interconnection, data center links, and secure transport in enterprise or industrial wide-area IP networks.
Does IPsec work with NAT?
Yes, but NAT can complicate native ESP handling. That is why NAT traversal mechanisms such as UDP encapsulation are important in many practical deployments.
Conclusion
IPsec encryption is best understood as the encryption-enabled part of a much broader network security framework. Its real value lies in the way it protects IP traffic using standardized policy control, peer authentication, negotiated security associations, and packet-level security services. When designed carefully, IPsec remains one of the most practical ways to secure communication between hosts, gateways, branches, clouds, and infrastructure domains across untrusted networks.