A Session Border Controller (SBC) is a network function deployed at the boundary between two communication networks to secure, control, and interconnect real-time sessions such as voice, video, and other SIP-based communications. In practical terms, it sits between domains such as an enterprise network and a service provider, a private UC system and a public SIP trunk, or an on-premises telephony platform and a cloud voice service. Its position at the network edge is what gives it both its name and its operational importance.
An SBC is not simply a voice gateway, and it is not only a firewall for VoIP. It is a specialized border element that understands signaling and media flows and can enforce communication policy at the edge of a network. Depending on the deployment, it may protect against SIP-based attacks, hide internal network topology, normalize signaling, anchor media, help sessions cross NAT boundaries, support encryption, and provide the demarcation point between internal and external real-time communications environments.
That is why SBCs remain central in modern enterprise telephony, SIP trunking, unified communications, carrier interconnect, Microsoft Teams Direct Routing, contact centers, and multi-site voice networks. They make real-time communications safer, more interoperable, and easier to control when traffic crosses trust boundaries.

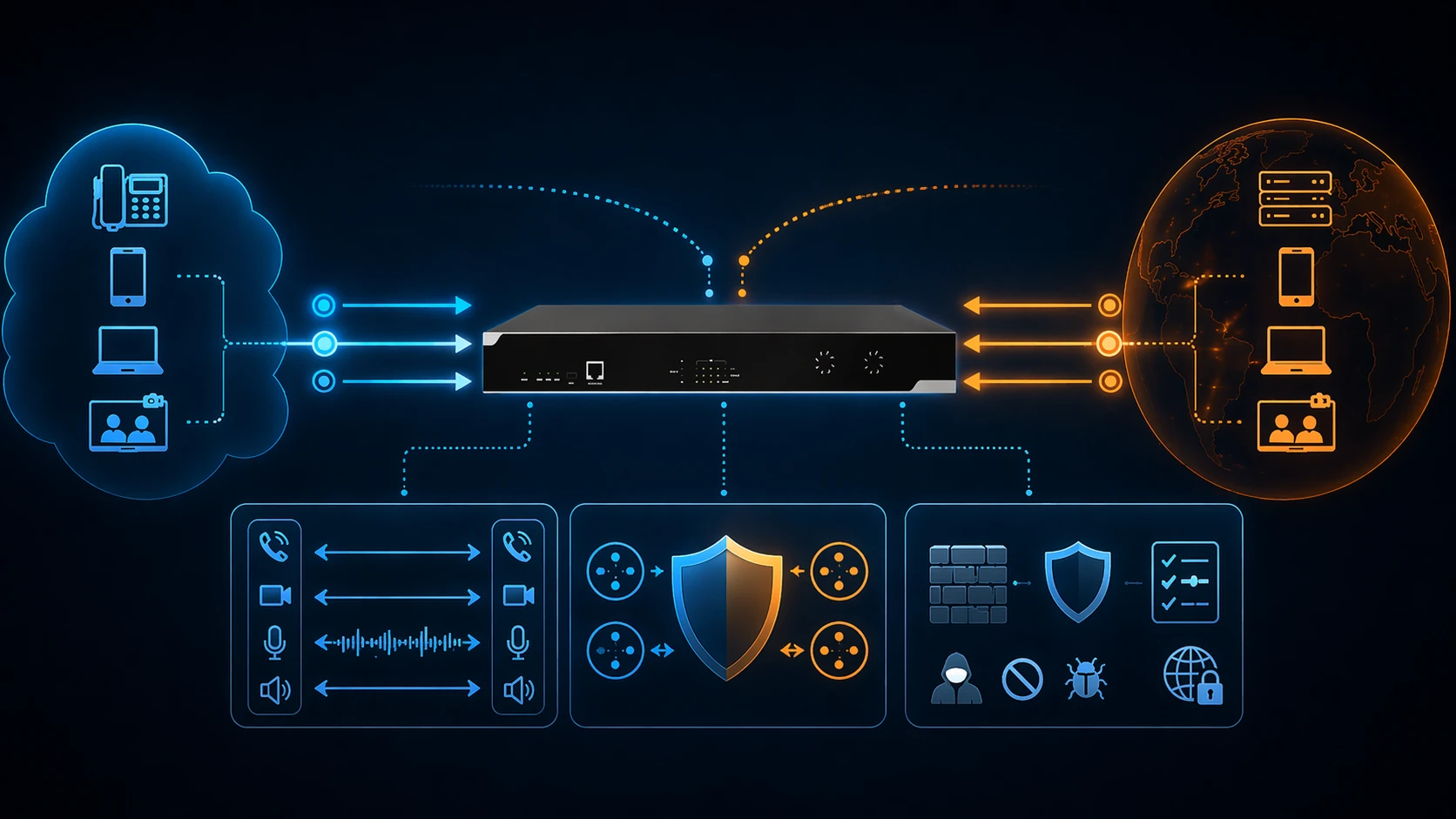
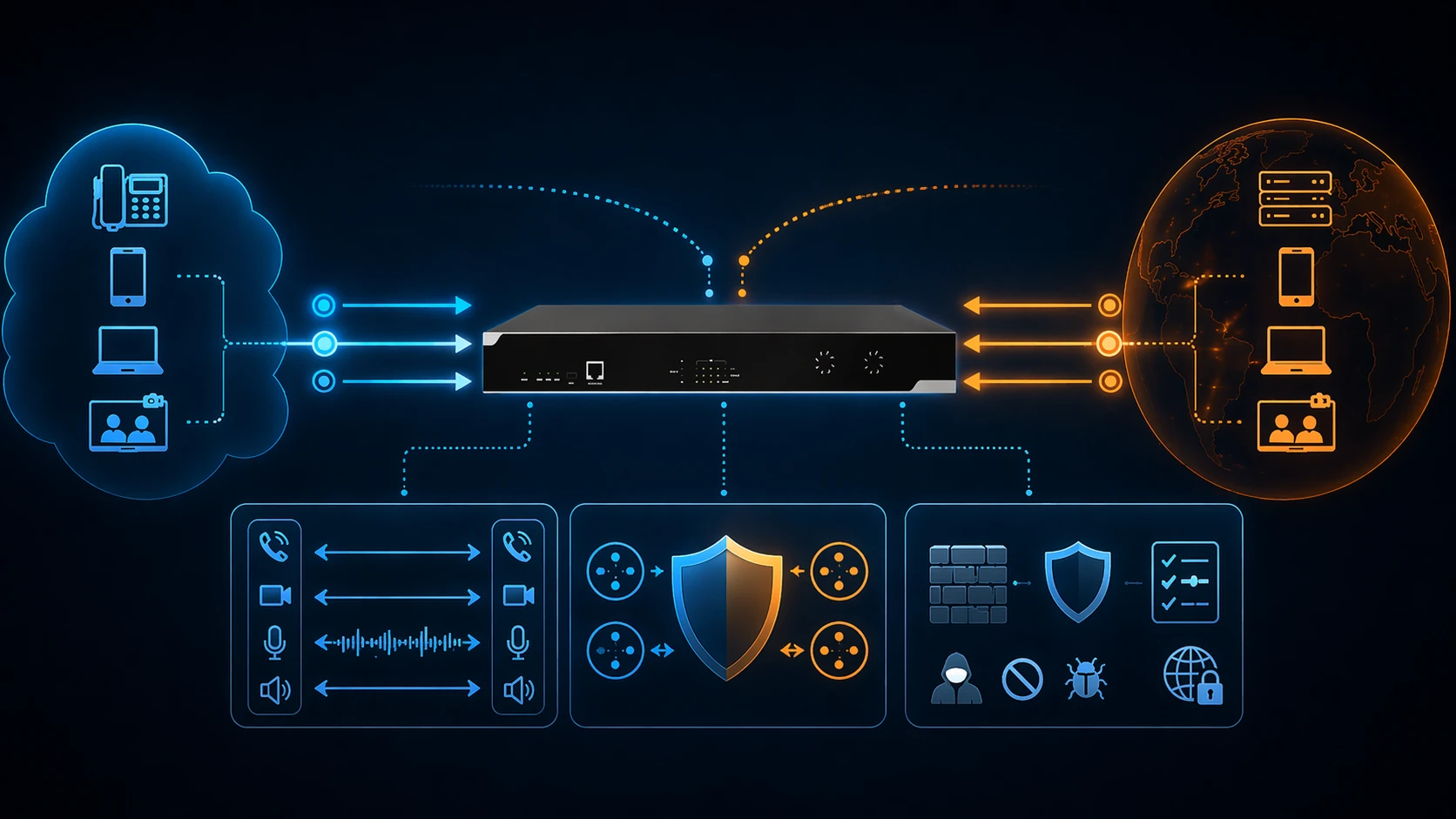
An SBC sits at the communication boundary and controls signaling and media as sessions pass between different IP networks.
What an SBC Means in Communications Architecture
A Border Element for Session Control
At its core, an SBC is a session-aware border element. It is deployed where two IP communication domains meet and where policy, trust, addressing, signaling behavior, or media handling may differ. Instead of allowing SIP and media traffic to pass directly from one domain into another with minimal control, the SBC becomes the managed interconnection point.
This role matters because real-time communications are different from ordinary web or data traffic. SIP signaling and media streams often depend on negotiated addresses, dynamic ports, codec alignment, identity trust, and timing-sensitive behavior. When those flows cross from an internal network to an external network, a specialized edge function is often needed to keep the communication secure and operationally reliable.
In this sense, an SBC is best understood as a communications demarcation and policy layer. It provides a controlled border where voice and multimedia sessions can be admitted, normalized, secured, and handed off appropriately.
More Than a Traditional Gateway
An SBC is often compared with a traditional gateway, but the two are not identical. A gateway commonly focuses on protocol or network conversion between different communication domains, such as TDM and IP. An SBC can support interworking, but its responsibilities are broader. It also enforces security, border policy, session admission behavior, and edge survivability for SIP and multimedia sessions.
This is one reason modern enterprise voice architectures frequently use SBCs even when the communications path is entirely IP-based. The value of the SBC is not limited to media conversion. Its value lies in secure interconnection and real-time session control at the boundary.
An SBC is best understood as the security and control point for real-time communication sessions at the edge of a network, not merely as a call-routing device.
How a Session Border Controller Works
It Sits in the Signaling and Media Path
In many deployments, the SBC is placed in the signaling path, the media path, or both. This allows it to examine SIP signaling, enforce policy, and decide how the session should be treated. In many enterprise and service-provider scenarios, it also anchors or relays media so that RTP streams do not travel directly between endpoints across the network boundary.
This placement gives the SBC deep control over the session lifecycle. It can inspect requests, modify headers, enforce routing logic, and help make sure the media path aligns with security and network policy. When the SBC anchors media, it can also simplify NAT traversal, improve visibility, and keep media exchange under controlled border governance.
This is why SBCs are often described as strategic edge devices or functions rather than passive forwarding elements. They actively participate in how the session is established and maintained.
It Terminates and Re-Originates Session Logic
Many SBC deployments operate using a back-to-back user agent style of architecture rather than behaving as a simple transparent proxy. In practical terms, the SBC terminates one side of the session signaling relationship and creates a new one toward the far side. This allows it to manipulate signaling, apply policy, and isolate internal network behavior from the external side.
This behavior is especially important for topology hiding, interoperability normalization, identity handling, and service policy enforcement. Because the SBC controls both signaling sides, it can adapt one side to the other without exposing the full internal logic of the private network.
This also helps explain why SBCs are so useful for SIP trunking and cloud interconnection. They provide a strong control layer rather than simply passing SIP messages through untouched.
It Applies Security and Policy at the Edge
Another core operating principle of an SBC is policy enforcement. The SBC decides which sessions should be allowed, how they should be routed, what headers or identities should be normalized, which encryption or admission rules apply, and how signaling and media should behave under load or attack conditions.
Because it sees sessions at the network edge, it can help protect internal systems from malformed signaling, unauthorized access, denial-of-service attempts, overload situations, and topology exposure. This is one of the main reasons SBCs are widely deployed between enterprise networks and external providers or public networks.
SBCs work by controlling session signaling and often media at the edge, allowing them to enforce security, interworking, and border policy.
Main Functions of an SBC
Security and Edge Protection
One of the most important functions of an SBC is protecting SIP and multimedia services at the network edge. SBCs are widely used to defend against SIP-based threats, signaling abuse, unauthorized access attempts, denial-of-service activity, and overload conditions. This is one of the clearest reasons enterprises and service providers deploy SBCs rather than exposing internal voice platforms directly.
In this role, the SBC strengthens the communications perimeter. It is not a generic data firewall replacement, but it adds a dedicated layer of protection for real-time communications traffic that general-purpose network tools may not handle as precisely.
This function becomes especially important in public SIP trunking, internet-facing voice services, and hybrid cloud communications where the trust boundary is exposed to external networks.
Topology Hiding and Privacy of Internal Networks
SBCs are also widely used for topology hiding. When signaling crosses the border, the SBC can conceal internal addressing, internal route structure, and private network details so that outside parties do not learn unnecessary information about the internal communications environment. This reduces reconnaissance value and strengthens privacy at the edge.
Topology hiding is one of the classic SBC functions because it fits naturally with the SBC’s border role and B2BUA-style control behavior. The external side sees the SBC-facing view of the session rather than the internal topology directly.
This is useful not only for security, but also for cleaner demarcation between administrative domains.
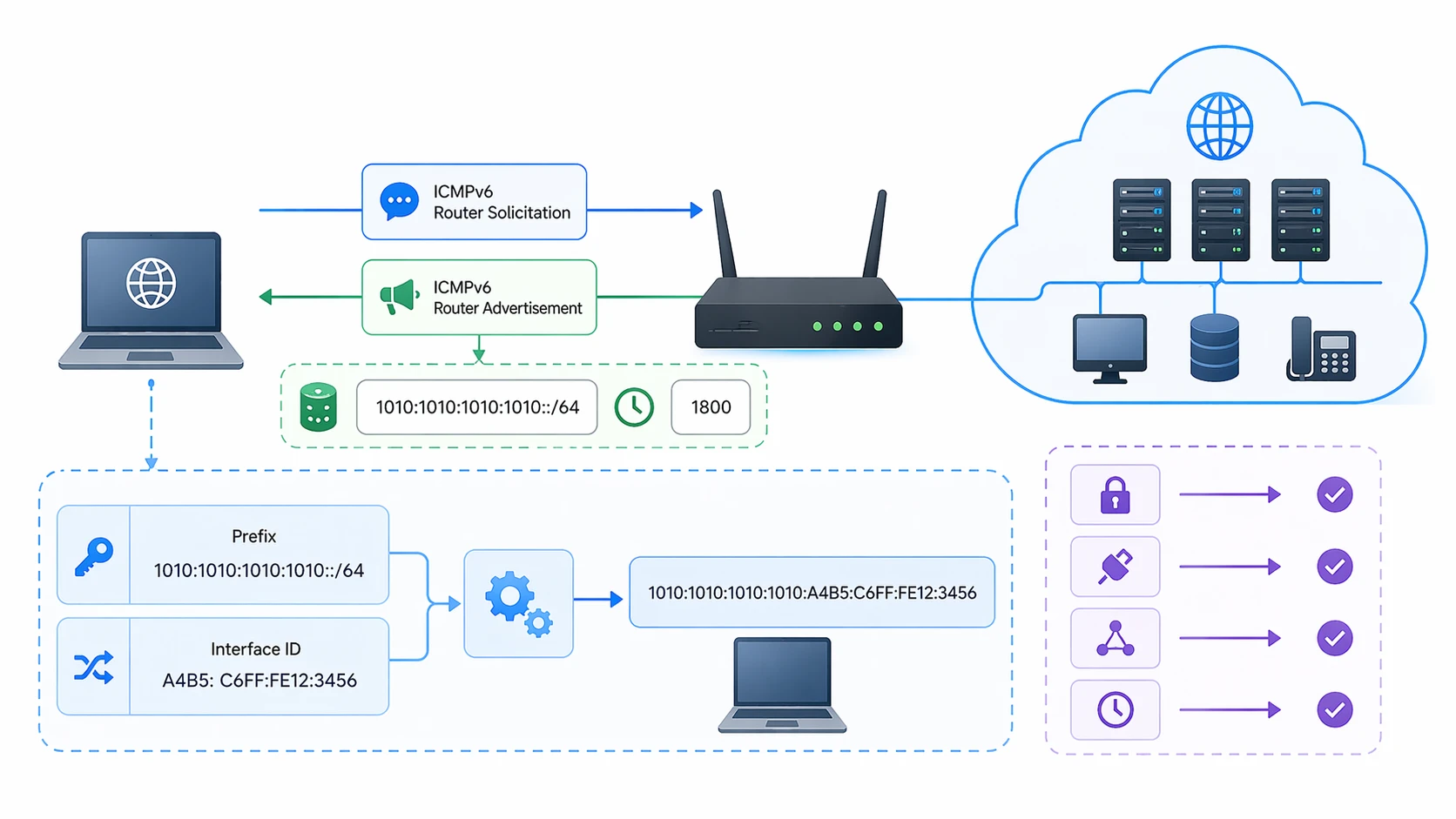
NAT Traversal and Media Anchoring
Real-time communications often have difficulty crossing NAT and firewall boundaries cleanly because signaling and media can use dynamically negotiated addresses and ports. SBCs commonly help solve this problem by anchoring signaling and media at the edge and relaying them through a controlled border point.
This is especially useful for remote users, SIP trunks, hybrid UC environments, and endpoints behind private addressing. The SBC can make externally reachable behavior consistent even when the internal endpoint addresses are not directly routable or when the media path needs tighter control.
NAT traversal support is one of the most practical reasons SBCs are deployed in everyday enterprise voice design, especially when phones, clients, or applications sit behind firewalls or private network edges.
Interworking and SIP Normalization
Another major function of an SBC is interoperability. Different carriers, PBXs, cloud services, and endpoints do not always implement SIP in exactly the same way. An SBC can normalize signaling, adjust headers, manage interoperability rules, and help one side communicate cleanly with the other.
This is valuable in SIP trunking, carrier peering, mixed-vendor UC environments, and cloud calling integrations. The SBC becomes the place where signaling differences are adapted instead of forcing every internal platform to accommodate every external variation directly.
In real deployments, this interworking function is often just as important as pure security. Without it, standards-based signaling may still fail in practice due to implementation differences.
The most important SBC functions usually come down to five themes: security, topology hiding, NAT traversal, media control, and interworking between communication domains.
Network Architecture of an SBC
Enterprise Edge Between PBX and SIP Trunk Provider
One of the most common SBC architectures places the device between an enterprise IP PBX or UC platform and an external SIP trunk provider. In this model, the SBC acts as the demarcation point between the internal communication domain and the external service-provider network. The enterprise side can keep its own numbering, routing, identity, and policy logic, while the SBC handles the border behavior toward the carrier.
This architecture is common because it reduces direct exposure of the PBX and gives administrators a central point for security, routing control, interoperability adjustments, and troubleshooting. It also makes provider changes and multi-trunk strategies easier to manage in many environments.
For SIP trunking, this remains one of the clearest examples of why SBCs are used in real deployments.
Cloud Voice and Direct Routing Interconnection
SBCs are also widely used in cloud voice interconnection. A well-known example is Microsoft Teams Direct Routing, where a supported customer-provided SBC connects Teams Phone to on-premises PSTN connectivity or SIP trunk services. In this design, the SBC acts as the enterprise-controlled border element between Microsoft’s cloud voice environment and the customer or carrier telephony side.
This architecture is useful because it lets organizations keep certain local telephony arrangements, providers, or regulatory models while still integrating with cloud collaboration and calling services. It also shows that SBCs remain highly relevant even when the broader communications stack has moved into the cloud.
In these deployments, the SBC is often the key technical bridge between modern cloud platforms and the existing voice network reality of the organization.
Service Provider and Peering Architecture
Service providers and large interconnect environments also use SBCs at network peering boundaries. In these scenarios, the SBC supports session control between service domains, helps enforce signaling policy, protects network resources, and manages the edge between organizations or carrier environments.
This is especially important because large-scale interconnection requires trust control, overload protection, numbering policy, media governance, and interoperability across different administrative domains. The SBC is a natural place to centralize those border functions.
As a result, SBCs are relevant not only inside enterprises, but also in carrier and service-provider architectures that support wider communication ecosystems.

SBCs commonly sit between internal UC or PBX systems and external SIP trunk, cloud, or carrier environments as the communications demarcation point.
Common Uses of SBCs
SIP Trunking Security and Demarcation
One of the clearest uses of an SBC is securing and managing SIP trunk connections between an enterprise and a telecom provider. The SBC acts as the controlled handoff point for signaling and media, protecting the internal network while helping ensure service interoperability and stable call setup.
This is one of the most common enterprise use cases because it maps directly to the need for both external voice connectivity and secure border control.
Unified Communications and Remote User Protection
SBCs are also used to support UC platforms, remote workers, and distributed communications environments. They can secure SIP audio and video traffic over the internet, help remote clients interact safely with internal communications systems, and keep external session flows from exposing the internal UC platform directly.
This role became even more important as organizations moved toward hybrid work and cloud-connected telephony. The SBC helps preserve border control even when users are not all inside one office network.
Cloud Voice Integration and Hybrid Calling
Another important use is connecting on-premises voice resources or carrier services to cloud calling platforms. This is common when organizations want to maintain certain PSTN, compliance, routing, or provider relationships while still adopting cloud telephony and collaboration tools.
In these environments, the SBC becomes the practical edge device that allows old and new communications models to work together in one architecture.
Applications of SBCs
Enterprise IP Telephony
In enterprise IP telephony, SBCs are used to secure the edge, support SIP trunks, hide internal topology, and manage interoperability between the PBX and external networks. This makes them highly relevant for offices, campuses, headquarters sites, and branch-based communications environments.
They are especially useful where the organization wants more direct control over voice security and demarcation than a generic network edge alone can provide.
Contact Centers and Compliance-Sensitive Voice Environments
Contact centers and regulated communication environments often use SBCs because they need stronger control over signaling, identity handling, DTMF privacy, trunk behavior, and carrier interworking. In these settings, the SBC helps create a more manageable and policy-driven border for business-critical voice traffic.
This application is especially important where service quality, privacy, and operational resilience all matter at the same time.
Service Providers and Multimedia Interconnect
Providers use SBCs in trunking, peering, hosted voice, and broader multimedia interconnect environments to protect their network edge and manage communication sessions between domains. The SBC helps maintain control even when many different customers, platforms, and communication paths interact with the provider environment.
This makes SBCs central not only to enterprise telephony but also to the wider voice and multimedia interconnection ecosystem.
Teams Direct Routing and Hybrid UC
Modern hybrid UC deployments also rely heavily on SBCs, especially in Microsoft Teams Direct Routing and similar interconnection models. Here, the SBC serves as the controlled SIP border that links cloud collaboration systems with PSTN connectivity, provider trunks, or existing enterprise telephony resources.
This application shows that SBCs are not only legacy telecom devices. They remain highly relevant in current cloud and hybrid voice architectures.
SBCs are most valuable anywhere real-time communications cross a trust boundary and need security, control, interworking, and policy enforcement at the edge.
Deployment Considerations and Best Practices
Match the SBC Role to the Real Border
The first design step is identifying the true communications boundary. In some environments, that boundary is between the enterprise and the SIP trunk provider. In others, it is between the cloud voice platform and the customer edge. In larger environments, there may be multiple borders that need different SBC roles.
Good SBC design begins with understanding where signaling and media leave one trust domain and enter another. That is where the SBC creates the most value.
Plan for Security, Interoperability, and Capacity Together
An SBC should not be selected only for signaling compatibility. Security controls, encryption behavior, NAT handling, media capacity, codec support, availability architecture, and operational visibility all matter. A deployment that solves one of these but ignores the others may still become fragile in production.
Because SBCs sit at the edge of business-critical communications, they should be planned as both a security function and a service continuity function.
Test Real Call Flows, Not Only Basic Registration
Successful SBC deployment requires testing beyond basic SIP registration or dial tone. Organizations should validate inbound and outbound call flows, failover behavior, codec negotiation, DTMF handling, topology hiding, media anchoring, encryption, and any required cloud or carrier interworking profiles.
This is especially important in mixed-vendor or hybrid-cloud environments where standards compliance alone may not guarantee seamless real-world behavior.
FAQ
What is an SBC in simple terms?
An SBC is a border device or network function that secures, controls, and interconnects SIP and real-time communication sessions between different IP networks.
Is an SBC the same as a voice gateway?
No. A voice gateway often focuses on media or protocol conversion, while an SBC adds security, topology hiding, policy enforcement, NAT traversal support, and border interworking for real-time communications.
Why is an SBC used with SIP trunks?
It is used to create a secure demarcation point between the enterprise and the provider, protect the internal network, normalize signaling, and control media and session behavior at the edge.
Can an SBC help with NAT traversal?
Yes. One of the common roles of an SBC is helping sessions cross NAT and firewall boundaries by controlling signaling and often anchoring media at the edge.
Where are SBCs commonly used?
SBCs are commonly used in enterprise IP telephony, SIP trunking, unified communications, contact centers, service-provider interconnect, Microsoft Teams Direct Routing, and hybrid cloud voice environments.